With Tanium as a Service, organisations can manage and secure distributed endpoints via a fully cloud-hosted-and-delivered solution SINGAPORE, July 23, 2020 — Tanium, the provider of unified endpoint management and security built for the world’s most demanding IT environments, today announced Tanium as a Service, a zero infrastructure endpoint management…
TrustKey Solutions Introduces New FIDO2 Key Line
DALLAS, July 20, 2020 — TrustKey Solutions ("TrustKey") announces T120 – FIDO2/U2F, USB-C security key. T120 is based on public key cryptography to protect users against phishing and man-in-the-middle attacks. T120 is a hardware security key for the consumers as well as enterprise deployments – it is fast, easy to…
Acronis Acquires DeviceLock, Adds Data Loss Prevention and Device Control to Growing Cyber Protection Portfolio
Singapore unicorn company adds DeviceLock’s leading device control and endpoint data loss prevention technology to further advance its business solutions SINGAPORE, July 16, 2020 — Acronis, a global leader in cyber protection, today announces the acquisition of DeviceLock, Inc., a leading provider of endpoint device/port control data leak prevention software for…
Strengthen Data Privacy on Your Website With Monsido
Monsido Empowers Website Owners to Take Control Of Personal Data on Their Website and Meet Regulatory Requirements SYDNEY, July 15, 2020 — Monsido, a leader in web governance solutions that enhance user experience, today announced the launch of their Data Privacy module. The new module will allow Monsido customers to automate…
Ivanti Wavelink Partners with Manhattan Associates to Support Windows to Android Migrations in Southeast Asia (SEA)
The Ivanti Rapid Platform will help validate multiple hardware platforms, providing the right solution for the right device SINGAPORE, July 14, 2020 — Ivanti Wavelink announced its partnership with Manhattan Associates, in support of Windows to Android migrations. Using Ivanti® Rapid Platform™, customers in warehousing,…
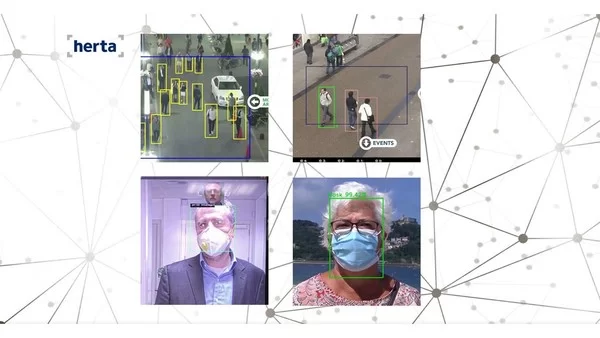
Herta Launches New COVID-19 Technology for the New Normality
The leading facial recognition firm launches new video analytics to enhance security and safety in the new post-pandemic era BARCELONA, Spain, July 13, 2020 — Herta, the Barcelona based facial recognition company, has recently launched a new range of solutions that will help businesses and industries adapt to the new normality….
The Critical Need for IoT Cybersecurity Will Drive Device Authentication Services to US$8.4 Billion Revenues by 2026
The increasing threat landscape is forcing IoT implementors and vendors to embrace and prioritize new hardware-focused digital security options LONDON, July 2, 2020 — By 2026, IoT connections will exceed 23 billion across all major IoT markets. Almost all those connections will be…
TUV Rheinland: Cyber risks for industrial plants underestimated
TUV Rheinland and Ponemon Institute publish worldwide study on the Cybersecurity of industrial plants. All information at https://go.tuv.com/otsurvey-2020 COLOGNE, July 2, 2020 — Cyberattacks can threaten the industrial facilities of companies even more than their IT systems. However, a holistic view of the security of industrial plants is often lacking….
YITU Technology received ISO/IEC 27701:2019 certification from BSI, becomes the first Chinese AI company to obtain it
SHANGHAI, July 1, 2020 — On June 30, 2020, YITU Technology, the world’s leading artificial intelligence (AI) company, received the ISO/IEC 27701:2019 certification from the British Standards Institution (BSI) for its privacy information management system, becoming the first AI company in China to…
RedShield appoints Senior Verizon Cyber Security VP as Chief Revenue Officer in U.S. Push
AUCKLAND, New Zealand, July 1, 2020 — RedShield, specialists in web application shielding, has announced the appointment of global cyber security leader, James Carrigan Jr. as Chief Revenue Officer (CRO), responsible for sales globally. Based in New York, Carrigan joins the cyber security challenger from Verizon Communications, where he…