Twitch experiences what cybersecurity experts are calling the largest breach in recent history. Here are all the details.
Vigilance is Crucial for Businesses in Dealing with Modern Malware
With ransomware evolving so quickly, businesses must be ever vigilant or risk losing their reputation and assets.
Popular Doesn’t Mean Safe – Google Pulls Apps from Play Store
Google pulls a number of apps from the Google Play Store after reports surfaced of them containing malware.
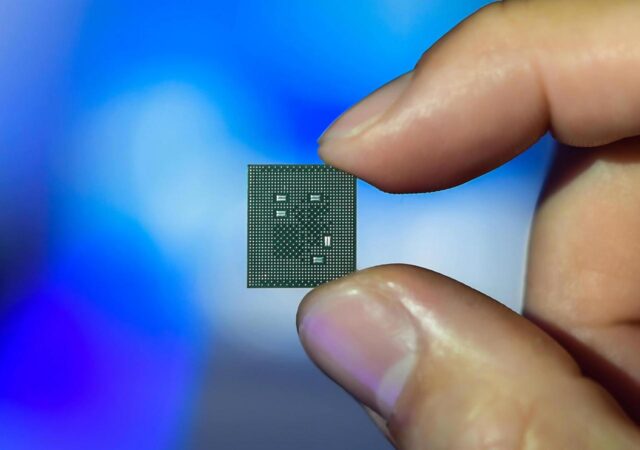
Qualcomm Processors Have A Worrying Security Flaw
Qualcomm’s processors are affected by a serious vulnerability which could put user data such as call logs, sms and even calls themselves at risk.
533 Million Facebook Users’ Data Resurfaces Online from 106 Countries
Facebook seems to be having a row of things recently. The company initially faced humongous backlash on their implementation of data sharing policies between popular messaging app, WhatsApp, and the larger company. Now, it looks like old wounds are reopening…
Aruba ClearPass Security Portfolio Recognised for Ability to Reduce Risk
Aruba ClearPass receives recognition from Marsh’s Cyber Catalyst program, making it the second of Aruba’s Cybersecurity offerings to be recongised.
Safeguard your Smartphone and Become a Cybersecurity Wiz
With an increase of cyberattacks worldwide, it’s time to look at one of our most used and most vulnerable devices: our smartphones.
Can cybersecurity keep up with flexible work arrangements?
As companies move to a remote workforce in light of the COVID-19 pandemic, they face an unprecedented cybersecurity risk as they are forced to widen their network. So what can companies do about it?