FSIs and other organisations are facing increased exposure when it comes to third-party risk – an aspect of cybersecurity that has gone unnoticed.
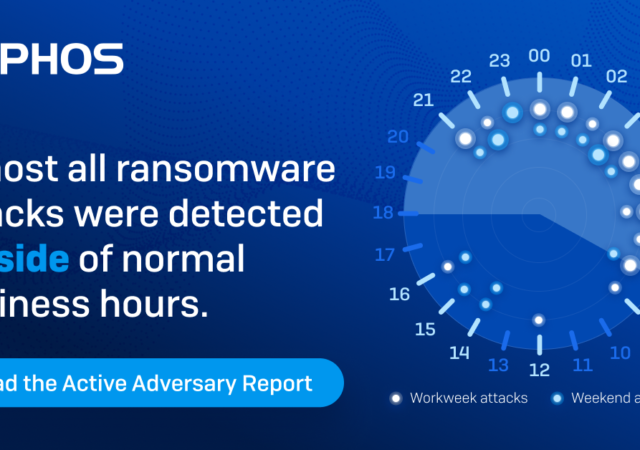
Sophos Report Reveals Dwell Time Shrinks to Just 8 Days in 2023
Cybersecurity company Sophos has recently released its Active Adversary Report for Tech Leaders 2023. The report highlights a few important findings about cyberattacks in the first half of 2023 as follows: 1) Decrease on Dwell Time Dwell time is basically…
Mozilla Enhances Online Privacy with Firefox Relay Integration
Mozilla integrates Firefox Relay into its Firefox browser as a native function allowing users to be able to take control of their privacy from the get go.
Email-based Phishing Attacks Up 464% in H1 2023
Acronis reveals a 464% rise in email-based phishing attacks and AI-driven cybercrime through its Mid-Year Cyberthreats Report 2023.
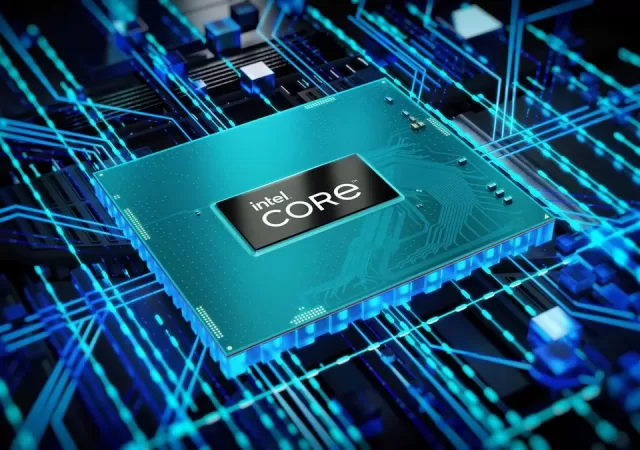
Downfall Vulnerability in Intel Chips Raises Security Concerns
A major Intel chip vulnerability named “Downfall” may allow hackers to gain access to temporary data storage and access sensitive information.
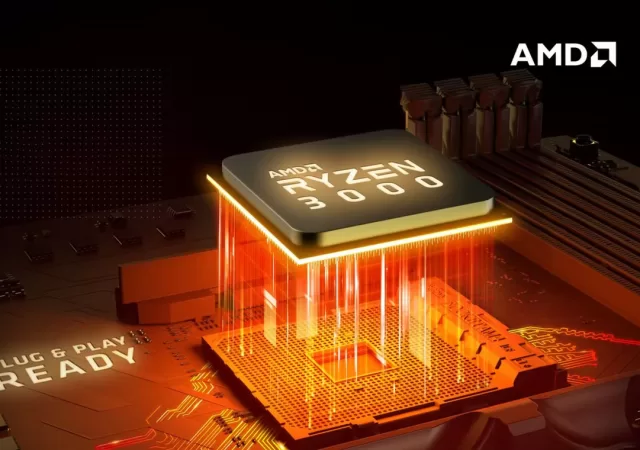
AMD’s Zen 3 & Zen 4 CPUs Are At Risk of Exploitations Thanks to New “Inception” Vulnerability
New Inception vulnerability in AMD Zen 3 and Zen 4 CPUs poses a security risk as it is reported to be able to leak sensitive data within 40 minutes on Linux.
Kaspersky Redefines End-Point Protection – Go Standard, Plus, or Premium
Kaspersky introduces their latest end-point cybersecurity solution – the Standard, Plus, and Premium protection plans.
Say Goodbye to Passwords with “Passkeys” for Google
Hacks, lost accounts and compromised emails may be a thing of the past with companies moving towards a “passwordless future”. Google is the latest to bring this future to the present with its introduction of “Passkeys”, a new way to…
ESET reports cyberthreats to Ukraine by Russian APT
Cybersecurity company ESET released its latest APT Activity Report, shedding light on coordinated threats to cybersecurity across the globe for 2022. Advanced Persistent Threats or APT, are broadly defined as targeted cyberattacks by either a single person or a coordinated…
Continuing the Pace of Government Innovation in a Post-Pandemic World
Government innovation is key to progressing a country. It cannot be spurred simply by world changing events. Instead, here are some ways that it can continue even now.