Sony Strikes a Balance Between Size & Aperture with New Wide-Angle Zoom G Lens FE 16-25mm F2.8 G
Experience the power of Sony’s new FE16-25mm F2.8 lens. Capture high-resolution images with beautiful bokeh, all in a compact and lightweight design.
-
Sony Announces New ULT Power Sound Line Up Complete with Wireless Headphones and a Tower Speaker
-
Sabahans Can Get 100Mbps Fibre Internet and Astro for as low as RM99.99 a month
-
Why Small Businesses Don’t Backup: Exploring Limitations and Solutions for Data Protection
-
Microsoft Unbundles Teams from Office 365 Globally
-
Samsung Details the Exynos 1480 Used in the Galaxy A55
-
Empowering Schools for The Digital Age


ASUS ZenBook Duo (2024) First Look | techENT


[VIDEO] Samsung Galaxy S24 Series First Look


[VIDEO] OPPO Reno 11 Pro Review


First Look at the Huawei MatePad Pro 13.2 & MateBook D16


OPPO Find N3 Flip First Look & Specs Rundown


OPPO Find N3 First Look & Specs Rundown


Unboxing the Lenovo Ideapad V14 (ASMR Edition)


Hands On with the Nothing Phone (2)
Sony Strikes a Balance Between Size & Aperture with New Wide-Angle Zoom G Lens FE 16-25mm F2.8 G
Experience the power of Sony’s new FE16-25mm F2.8 lens. Capture high-resolution images with beautiful bokeh, all in a compact and lightweight design.
Touch ‘n Go eWallet to Charge 1% Fee on International QR Transactions
Touch ‘n Go eWallet is one of Malaysia’s largest eWallets. Just recently, TNG Digital (TNGD), the company operating the eWallet, unveiled plans to become an integrated fintech company – one of the first in Malaysia. TNGD is well on the…
Samsung Reprices Galaxy Tab S9 & Galaxy Tab S9 FE in Malaysia
Samsung’s popular Galaxy Tab S series is getting more affordable. No, Samsung didn’t release another edition of the series. Instead, the tablet lineup is getting a price adjustment. The prices are taking effect starting on April 9, 2024. The Galaxy…
Sony Announces New ULT Power Sound Line Up Complete with Wireless Headphones and a Tower Speaker
Sony announces the new ULT Power Sound lineup that comes with a party speaker, headphones and portable speakers.
Sabahans Can Get 100Mbps Fibre Internet and Astro for as low as RM99.99 a month
Astro brings exclusive offers to Sabah on the heel of the finalization of its agreement with Celcom Timur Sabah.
Why Small Businesses Don’t Backup: Exploring Limitations and Solutions for Data Protection
Discover the best backup solutions for your business. Explore the 3-2-1 rule and find alternatives to protect your data without breaking the bank.
Microsoft Unbundles Teams from Office 365 Globally
Microsoft unbundles Microsoft Teams from Microsoft 365 and Office 365 globally preempting administrative measures from the EU and other governments.
Samsung Details the Exynos 1480 Used in the Galaxy A55
Samsung finally unveils the details behind the Exynos 1480 processor which launched with the recently launched Galaxy A55.
Empowering Schools for The Digital Age
In recent years, rapid technological advancement and shifting societal needs have evolved the educational landscape significantly. Technology now plays an integral part in revolutionising traditional learning methods, offering new avenues to enhance teaching and learning modes. Schools must comprehend and…
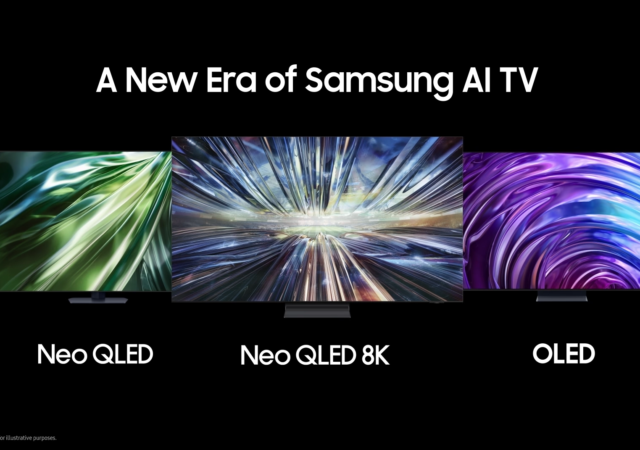
Samsung Launches New TV Lineup With AI Front and Center
Samsung announces its 2024 lineup of Neo QLED 8K, Neo QLED and OLED TVs with a new generation of processors and AI features.


The Sony Xperia 1 V In-Depth Review – Maybe the Best MYR 6,399 You Can Spend
Sony’s Xperia 1 V is a thing of understated beauty to us. We really like it, but we also think that it is not made for everyone.


HP Pavilion Plus 14 AMD 7840U Review
Great for general work (typing and browsing), photo editing, casual video editing, light to moderate gaming, traveling, and watching videos, the HP Pavilion Plus 14 AMD 7840U doesn’t breaking the bank. Perfect for those who move about a lot for work and students, especially when on sale.